Why no one should be surprised by the Facebook / Cambridge Analytica “breach”
As I’m someone who is concerned about privacy and the invasiveness of technology in our lives, you might be startled by my response to the alleged “data breach” in the Facebook / Cambridge Analytica saga. My reaction: “It’s not a breach if data was supplied with consent!” Of course, the important word is “if”. How... Read More.
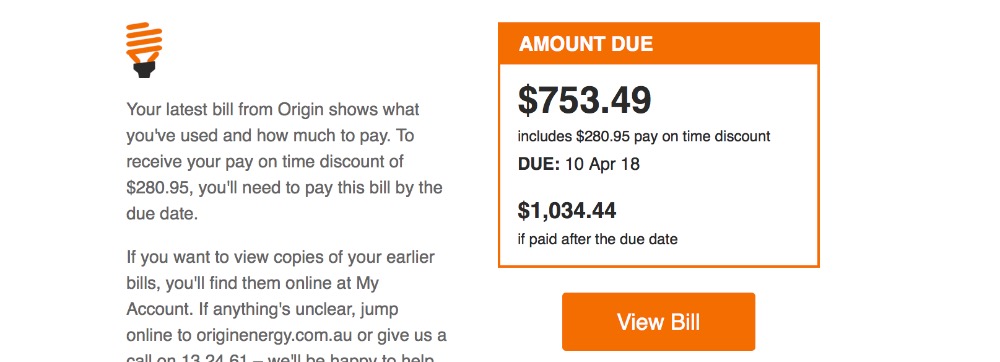
Origin Energy phishing alert – do not pay any bills until you read this post!
Today I received an email that looked like a bill from Origin Energy. It looked very authentic – there was good attention to detail, and I’m sure that this will deceive many people. Do not pay any bill from Origin until you learn how to identify a fake I’ll cover several ways to spot a... Read More.
ROCA Rocks the Crypto Industry That Was KRACK’d Only Days Ago
The security/cryptography industry has recently taken a battering. Hot on the heels of the KRACK WiFi network vulnerability comes an even bigger, more calamitous and more widespread hazard – the ROCA hack has exposed millions of smartcards, laptops, devices and secure systems to potential criminal activity. Infineon Technologies AG is a multi-billion dollar, 18-year old... Read More.
Every WiFi Network in the World is Potentially at Risk
They have called it KRACK — Key Reinstallation Attack – and it uncovers a vulnerability in practically every modern WiFi network in the world. The flaw lies at the heart of the WPA2 security protocol that controls access and encrypts traffic. It can be leveraged to snoop on confidential information such as emails, credit card... Read More.
Here’s How Cybercriminals Stole $100 Million From EU Banks and Vanished Without Trace
A wave of financially-motivated cybercrime has hit European and former Soviet banks to reveal profound security weaknesses in the technology infrastructure that handles transactions and funds worth billions of dollars. But how do we stop the next generation of tech-savvy criminals? What security measures must institutions enact to prevent further hemorrhaging of funds in the... Read More.
Petya: A Useless Ransomware that Wreaked Havoc
On June 27, 2017, opportunistic cybercriminals took advantage of exploits leaked by Shadow Brokers, a group that had previously released cyberweapons used by the National Security Agency. The latest exploit was a variant of Ransom: Win32/Petya that was initially seeded through the update mechanism of an accounting software program used in Ukraine. Since then, the... Read More.